Cybersecurity threats are evolving at an unprecedented rate, with organizations facing increasingly sophisticated risks that can compromise sensitive data and critical infrastructure.
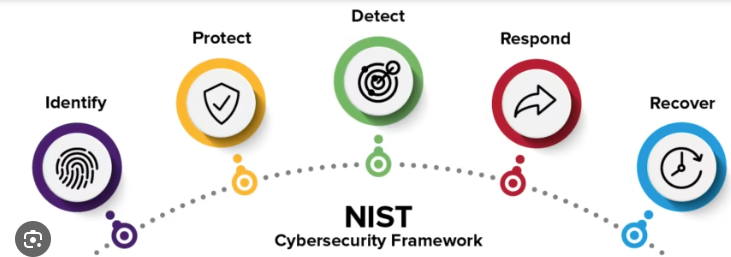
Enter the NIST Risk Management Framework (RMF) can be separated into five parts
- Understanding NIST
- NIST process steps
- Who uses NIST
- NIST Implementation Strategies
- NIST Challenges and Solutions
Did you know that in 2023, the average cost of a data breach reached a staggering $4.45 million? The NIST RMF isn’t just a framework; it’s your organization’s strategic blueprint for navigating the complex landscape of cybersecurity risk management.
Understanding the NIST Risk Management Framework
The NIST Risk Management Framework (RMF) represents a critical cybersecurity strategy designed to help organizations systematically identify, assess, and mitigate cyber risks through a structured, comprehensive approach.
Originally developed by the National Institute of Standards and Technology, this framework provides federal agencies, defense contractors, and information security professionals with a robust methodology for managing complex cybersecurity challenges by establishing a standardized seven-step process that enables continuous monitoring, risk-based decision-making, and adaptive security control implementation.
By categorizing systems, selecting appropriate security controls, and maintaining ongoing risk assessment, the NIST RMF distinguishes itself from traditional risk management approaches through its proactive, holistic methodology that emphasizes compliance, security governance, and strategic risk mitigation across diverse technological environments.
Organizations leveraging the NIST RMF can effectively navigate increasingly sophisticated cyber threats, align with federal regulations like FISMA, and build a resilient, responsive information security ecosystem that protects critical assets and minimizes potential vulnerabilities.
The 7 Comprehensive Steps of NIST RMF
The NIST Risk Management Framework (RMF) delivers a strategic cybersecurity roadmap through seven critical steps that transform organizational risk management.
- Prepare: Identify and prioritize organizational risk at the enterprise and mission/business process levels
- Categorize: Categorize the system and information processed, stored, and transmitted based on impact analysis
- Select: Select baseline security controls for the information system, tailoring and supplementing as needed
- Implement: Implement the selected security controls and document how they are deployed
- Assess: Assess the security controls using appropriate assessment procedures to determine control effectiveness
- Authorize: Determine the risk to organizational operations and assets, and decide whether to authorize the system
- Monitor: Continuously monitor the security controls, conducting ongoing assessments to ensure continued effectiveness and identifying potential changes that could impact the system’s security posture
Organizations begin by preparing their risk strategy, carefully categorizing systems based on security impact levels, and methodically selecting appropriate security controls that align with their specific risk profile.
The implementation phase focuses on documenting selected controls in a comprehensive System Security Plan (SSP), followed by an in-depth assessment to validate control effectiveness and identify potential vulnerabilities.
Senior leadership then authorizes system operation through a formal Authorization to Operate (ATO), establishing a continuous monitoring process that enables adaptive, real-time risk management.
These interconnected steps create a dynamic framework for proactively addressing cybersecurity risks, ensuring organizations can effectively identify, assess, and mitigate potential threats while maintaining compliance with federal security regulations and industry best practices.
Who Needs the NIST Risk Management Framework?
The NIST Risk Management Framework (RMF) is a critical cybersecurity strategy essential for government agencies, defense contractors, federal information systems, and private sector organizations seeking robust risk management solutions.
From healthcare and finance to technology and critical infrastructure, organizations across diverse industries benefit from RMF’s comprehensive approach to identifying, assessing, and mitigating cybersecurity risks, ensuring compliance with federal regulations like FISMA and FedRAMP.
Whether you’re a federal contractor handling sensitive data, a private enterprise looking to enhance security governance, or an organization aiming to implement strong information system controls, the NIST RMF provides a standardized, adaptable framework that supports continuous monitoring, risk assessment, and strategic security control implementation across multiple sectors and organizational types.
Implementation Strategies for NIST RMF
Implementing the NIST Risk Management Framework (RMF) requires a strategic, comprehensive approach that transforms organizational cybersecurity practices.
Organizations must focus on critical implementation strategies, including comprehensive risk assessment tools, robust security control selection, and building a proactive risk management culture that prioritizes continuous monitoring and skill development.
By leveraging specialized cybersecurity training, developing adaptive implementation resources, and creating a systematic approach to risk identification and mitigation, companies can effectively align their security strategies with the NIST RMF’s seven-step process.
Leveraging will ultimately improve their cyber resilience, ensuring regulatory compliance, and proactively addressing evolving digital threats through a structured, methodical framework of ongoing risk evaluation and strategic security control implementation
Common Challenges and Solutions in NIST RMF
Implementing the NIST Risk Management Framework (RMF) presents organizations with multifaceted cybersecurity challenges that require strategic navigation.
Businesses often encounter significant implementation barriers, including organizational resistance, complex compliance requirements, and resource constraints in cybersecurity risk management.
Successful RMF adoption demands cost-effective approaches that address potential obstacles through comprehensive risk assessment methodologies, robust security control selection, and continuous monitoring strategies.
By leveraging case studies of effective implementations, organizations can develop tailored solutions that align with their unique risk tolerance, enabling them to overcome technical, cultural, and financial hurdles in establishing a proactive cybersecurity governance framework that meets federal information security standards and protects critical information systems.
The NIST Risk Management Framework isn’t just a compliance checklist – it’s a comprehensive strategy for building cyber resilience. By embracing this framework, organizations can transform their approach to cybersecurity, turning potential vulnerabilities into strategic advantages.
Ready to revolutionize your cybersecurity strategy? Start your NIST RMF journey today and protect your organization’s most critical assets!





